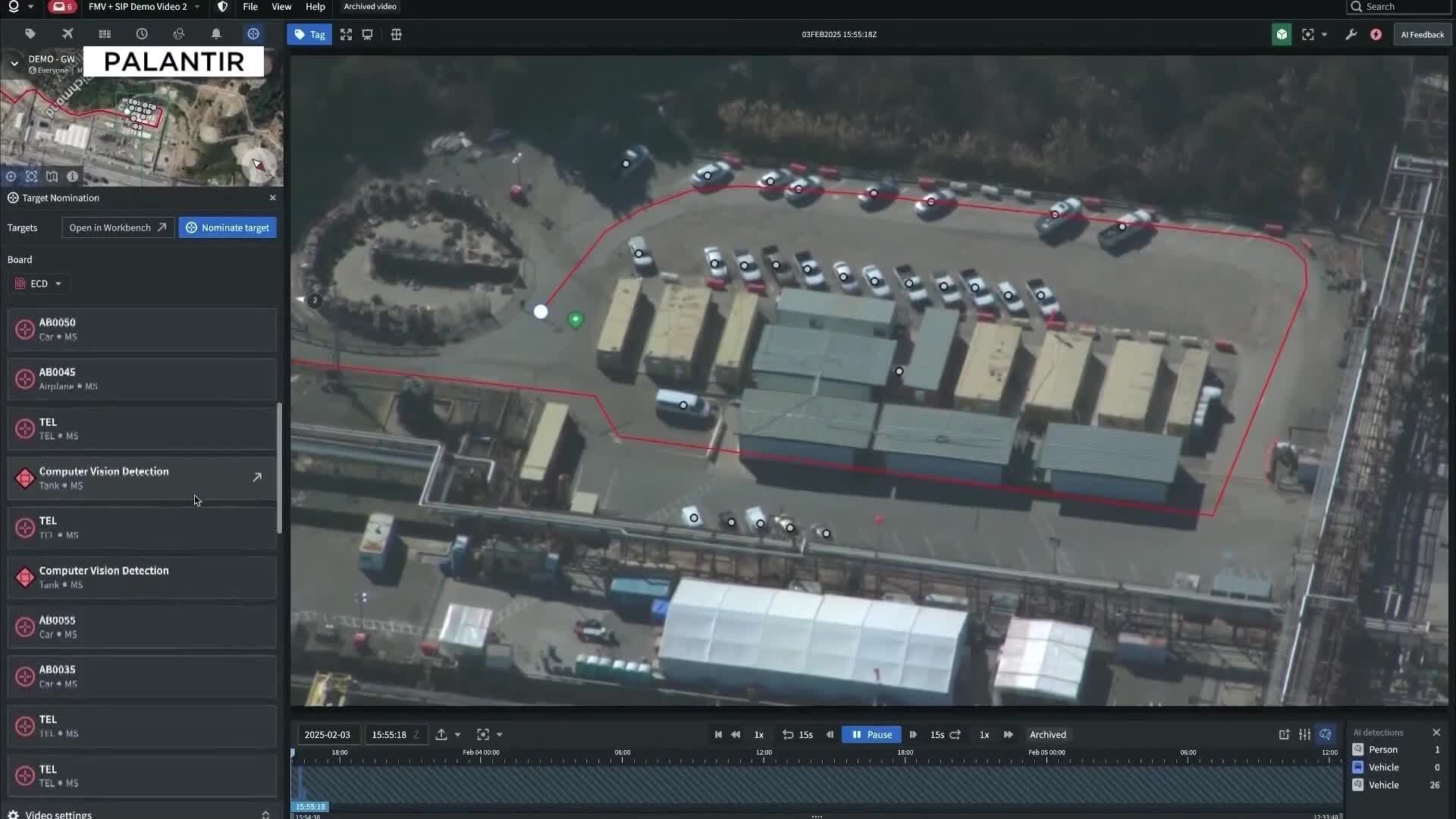
 The evolving landscape of modern warfare has introduced a surprising new category of high-value military targets: data centers. Recent events have underscored this shift, with Iranian drones striking three data centers in the United Arab Emirates and Bahrain. Following these attacks, Iran's Revolutionary Guard Corps publicly identified 29 tech targets operated by major companies like Google, Microsoft, and Palantir, and even released a video threatening a specific $30 billion data center operated by OpenAI.
The evolving landscape of modern warfare has introduced a surprising new category of high-value military targets: data centers. Recent events have underscored this shift, with Iranian drones striking three data centers in the United Arab Emirates and Bahrain. Following these attacks, Iran's Revolutionary Guard Corps publicly identified 29 tech targets operated by major companies like Google, Microsoft, and Palantir, and even released a video threatening a specific $30 billion data center operated by OpenAI.
Emily Harding, director of the Intelligence, National Security and Technology program at the Center for Strategic and International Studies (CSIS), characterized these attacks as a "sea change in warfare." Harding, who previously held senior positions at the CIA and the National Security Council, emphasizes that this development necessitates new policy approaches from the United States.
The Strategic Importance of Data in Modern Conflict
"Data is the new way of war," Harding explained, highlighting its indispensable role in contemporary military operations. She elaborated on the latest episode of Generation AI that modern warfare, particularly with the advent of AI-powered systems like the Maven Smart System, relies heavily on vast amounts of data and significant computing power. Data centers, therefore, have become critical infrastructure, underpinning these advanced military capabilities.
Adding to their vulnerability, data centers are often characterized as "relatively soft targets." Typically designed to be civilian infrastructure, they are not heavily fortified. Harding described them as "big warehouses, basically," which "don’t necessarily have a lot of defenses around them." This makes them attractive and accessible targets for adversaries seeking to disrupt an opponent's technological advantage.
Lessons Learned from the Ukraine Conflict
The critical role of data centers in conflict first became acutely apparent during the war between Russia and Ukraine. Harding noted that Ukrainian authorities recognized early on that data centers would likely become targets for the Russian government. In response, Ukraine enacted legislation permitting the relocation of sensitive data to facilities located in other countries.
Russia, Harding observed, showed a degree of reluctance to directly attack these data centers, particularly those situated within NATO member states. Instead, Russia primarily focused its efforts on cyber attacks and targeting data within Ukraine's borders.
"The Iranians, however, have had no such compunction," Harding stated, referring to the willingness of Iran to target data centers in the UAE and Bahrain, viewing them as legitimate targets if they were perceived to be supporting the American war effort.
The Legality of Targeting Data Centers
The drone strike on a data center at Bank Sepah in Tehran has ignited a complex debate regarding the legality of targeting such facilities under international law. Harding acknowledged this as a "very difficult legal question."
The bank in question was reportedly responsible for processing payments to the IRGC, which, from one perspective, could classify it as a military target. However, Harding also pointed out that it also serves as a civilian bank. This duality raises the question of whether such targets are considered dual-use, blurring the lines between military and civilian infrastructure.
"What it really does is put data center companies in a position where they’re going to have to think about themselves differently," Harding remarked, suggesting that these companies may need to re-evaluate their security postures and their role in a potentially militarized digital landscape.
Threats to Domestic Data Centers and Arizona's Role
Arizona stands out as a major hub for data center development within the United States. According to Pew Research, the state currently hosts 98 operational data centers, with an additional 86 planned or under construction. This significant concentration of digital infrastructure makes it a potential target.
Harding outlined two primary avenues for attacks on data centers: kinetic attacks and cyber attacks. A kinetic attack, such as a drone strike or missile strike, on a U.S. data center by a hostile nation like Russia or Iran would represent a "significant escalation."
In contrast, cyber attacks are considered a far less escalatory form of aggression. "There’s probably a much lower bar to do something like that," Harding noted. This lower barrier to entry for cyber warfare means that "that's where the U.S. government is going to have to make some decisions about exactly how they view this infrastructure."
Strategies for Protecting Data Centers
Harding proposed a three-pronged approach for the U.S. government to bolster the security of data centers:
-
Enhanced Intelligence Sharing: The government currently has a "duty to warn" companies if it learns they are specifically targeted, but this threshold requires "actionable and specific" information. Harding advocates for the intelligence community to "open up those taps and share more information" with data center operators, providing them with earlier and more comprehensive threat awareness.
-
Acting as an Insurer of Last Resort: In situations where insurance policies might void coverage due to acts of war, the U.S. government could step in as a backup insurer. This would provide crucial financial assurance to tech companies, ensuring their assets are protected even in the event of conflict-related damages.
-
Establishing Deterrence Through Messaging: A clear message to potential adversaries is essential. The U.S. government should communicate that any attack on a data center will be considered a direct attack on the United States, thereby raising the stakes for any hostile action.
"The three of these things together, I think, would be a pretty good safety net for these companies," Harding concluded.
Beyond government initiatives, Harding also suggested that countries in the Gulf region could consider enacting legislation to relax restrictions on private entities deploying anti-drone capabilities. This could help distribute the burden of protection, allowing companies to more proactively defend their critical data infrastructure.

No comments:
Post a Comment